Data generation and sharing have reached unprecedented levels in today’s digital landscape. The need to uniquely identify and efficiently manage data has become more critical than ever before. The term “UID” stands for “Unique Identifier Data.” The UID number is used to identify each user or product and is usually assigned by an application that processes the data. Unique identifiers are typically assigned to anything that needs to be distinguished from other entities, such as individual users, companies, machines, or websites. These distinctive values can either be randomly auto-generated with an algorithm or allocated incrementally by the user.
Uniquely Identifying Data: What It Means
Uniquely Identifying Data involves assigning unique identifiers, such as codes or tags, to individual data elements. These identifiers act as digital fingerprints or signatures, distinguishing one piece of data from another. UID is essential for maintaining data integrity, accuracy, and traceability. It enables organizations to efficiently manage and leverage data across various systems and applications while ensuring data security and privacy.
The UID has become a way to better track the assets of the United States Department of Defense. Every asset that is purchased or owned by the government gets a serial number that will be associated with it throughout its entire useful life. This serial number is presented in a rectangular 2D barcode called a data matrix code. Although it can be read by a scanner, this code looks different than what is usually associated with barcodes—it doesn’t have spaces and bars in it; instead. It has boxes that each contain four characters: two digits and two letters. This distinct marking was established by Department of Defense Standard Practice 130, “Identification Marking of U.S. Military Property,” in 2004.
Techniques for Effectively Tracking and Linking Data
Efficiently Tracking and linking data is crucial for seamless data management. Let’s explore some effective techniques to achieve this:
- Data Mapping and Categorization: Data mapping involves systematically representing data relationships. Organizations can establish clear connections and dependencies between datasets by categorizing and mapping data elements based on unique identifiers. This technique aids data lineage, improves visibility, and enhances overall data management processes.
- Data Tagging and Indexing: Data tagging involves attaching metadata or labels to individual data elements. Organizations can categorize and classify data based on various attributes by assigning UIDs as tags. Indexing the tagged data further improves search capabilities, enabling quick and efficient access to specific elements. Data tagging and indexing simplify data retrieval, supporting faster decision-making processes.
- Data Profiling and Deduplication: Data profiling involves analyzing data elements to identify patterns, inconsistencies, and quality issues. Organizations can detect duplicate data entries by examining unique identifiers and performing data deduplication. Eliminating redundant data enhances data quality, optimizes storage resources, and improves overall system performance.
- Data Integration and Linkage Platforms: Advanced data integration and linkage platforms can greatly enhance data tracking and linking capabilities. These platforms provide automated tools and algorithms to match and merge data from multiple sources based on unique identifiers. They streamline the process, reduce manual effort, and ensure accurate and efficient data integration.
- Master Data Management (MDM) Systems: Implementing MDM systems helps establish a single, authoritative source of master data. Unique identifiers play a key role in MDM, as they enable the identification and synchronization of master data across different systems and applications. MDM systems provide a central hub for tracking, linking, and managing data, ensuring consistency and reliability throughout the organization.
Uses of UIDs
UIDs are used in many ways, the most common being when users register for a website or service. These UIDs help companies keep track of their user’s data and make it easier to sort and filter through information.
UIDs can make sorting and filtering information easier, and help trace information back to specific users or entities within the system. The same can be done in a physical supply chain when manufacturers mark individual pieces of a larger component with a serial number. You can also use them to track the origin of a product in case of a malfunction, defect, or recall.
The healthcare industry also relies on unique identifiers, such as personal codes. These codes help to prevent patient privacy issues and eliminate duplicate reports.
UID Examples
There are a variety of ways to implement a Unique Identifier Data on the Internet, a few examples include:
- Uniform Resource Identifier (URI) – A URI is a unique identifier that makes content addressable on Web pages.
- Uniform Resource Locator (URL) – URLs are specific types of URIs that target Web pages so that when a browser requests them, they can be found and served to users.
- Universal Unique Identifier (UUID) – A UUID is a number that uniquely identifies a particular object or entity on the Internet.
- Global Unique Identifier (GUID): GUIDs are generated by Microsoft programming and have many uses, including for Word documents.
- Bank identifier Code (BIC): A BIC is a unique identifier issued by banks to identify each other.
- Unique Device Identifier (UDID): A UUID is a 40-character string that’s assigned to a particular device, such as an iPhone or iPad.
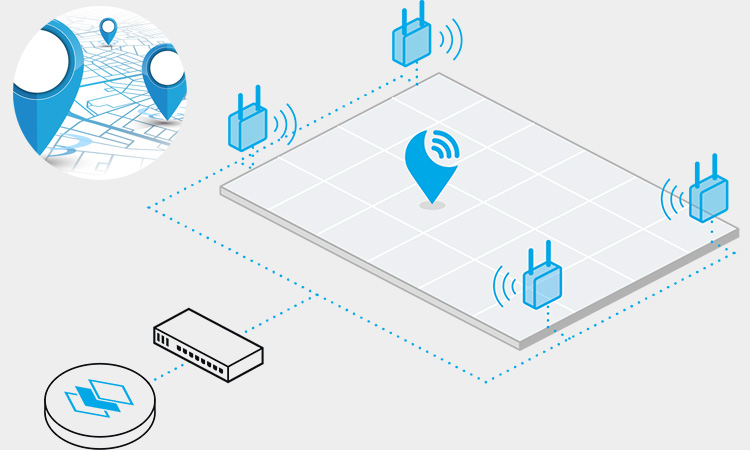
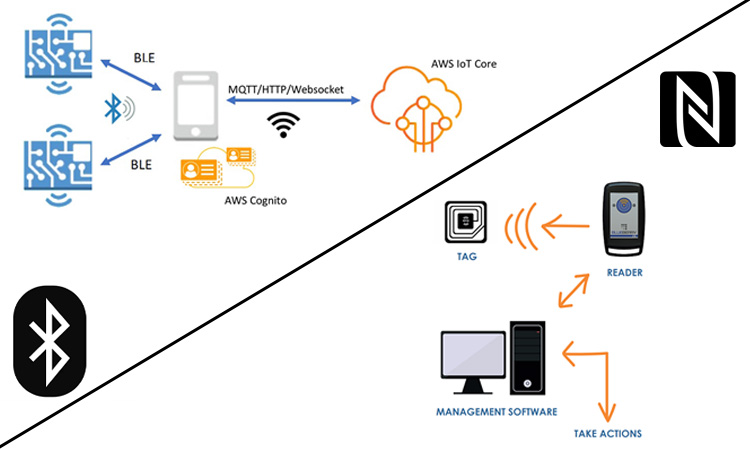
- Service Set Identifier (SSID): A SSID is a sequence of letters that identifies the name of a wireless network.
UID vs IUID vs UII
The Department of Defense has three related acronyms: the Item Unique Identification (IUID) Registry, the UII, and the UID.
The IUID Registry stores information on how to track and maintain government assets. Items are added to this registry if their acquisition cost is over five thousand dollars, they are mission critical or they are high risk. The UII refers to an item’s unique identifier that is typically machine-readable and helps contractors track each item digitally through all stages of its lifecycle. An item’s UID is the physical marking on an item that distinguishes it from other items.
Related Articles: What is IUID (Item Unique Identification)?
UID, IUID, and UII are Difference
The Defense Procurement and Acquisition Policy clarifies the differences between UIDs (unique item identifiers), IUIDs (identification unique items), and UIIs (unique item identifiers).
UID/IUID is a system of unique identifiers established by the Department of Defense. It provides a way for people to identify military equipment and supplies, and it helps prevent theft and loss.
The UII is a globally unique and unambiguous identifier that distinguishes an item from all other like and unlike items. It is derived from a UII data set that contains one or more data elements.
The MIL-STD-130 (DOD) document provides uniform engineering and technical requirements concerning processes, procedures, practices, and methods. Specifically, it addresses standard practices for identification marking for U.S. military property—both for UID applications and for non-UID applications.
Related Articles: What is a UII(Unique Item Identifier)?
Importance of UIDs in Data Management:
UIDs play a crucial role in effective data management. Let’s explore why they are essential:
Ensuring Data Integrity and Accuracy
UIDs help maintain data integrity by distinguishing individual data elements. They prevent errors, duplicates, or inconsistencies in data, ensuring a reliable and consistent source of information. With accurate and reliable data, organizations can make informed decisions and drive business success.
Enabling Efficient Data Integration
Data integration involves combining data from diverse sources to create a unified view. UIDs facilitate the seamless merging of data by enabling data matching and linking. This integration allows organizations to gain comprehensive insights and a holistic understanding of their information landscape.
Enhancing Data Security and Access Control
Unique identifiers contribute to data security and access control. Organizations can implement granular access controls by associating data elements with UIDs, ensuring that only authorized individuals can access specific data. In case of data breaches or unauthorized access, UIDs enable traceability, making identifying and mitigating potential risks easier.
Streamlining Data Analysis and Retrieval
Unique identifiers simplify data analysis and retrieval processes. Organizations can categorize and organize information effectively by assigning unique identifiers to data elements. This categorization enables quick and accurate retrieval of specific data elements, improving operational efficiency and accelerating decision-making processes.
Supporting Data Integration and Collaboration
Unique identifiers foster data integration and collaboration among different systems and teams. Consistent identifiers allow data from various sources to be easily linked and shared, enabling cross-functional collaboration and enhancing data-driven insights.
Facilitating Data Governance and Compliance:
nique identifiers contribute to effective data governance and compliance. They enable traceability, auditing, and accountability, ensuring adherence to regulatory requirements and data governance policies. This facilitates transparency and establishes trust among stakeholders.
Balancing Data Privacy and Data Integration
Finding the right balance between data privacy and integration is a critical challenge in today’s digital landscape. Here’s why it’s important and how organizations can navigate this delicate equilibrium:
Protecting Individual Privacy Rights
Safeguarding personal information and respecting privacy rights is paramount for organizations. Balancing data integration and privacy ensures that individuals’ sensitive data remains secure, preventing unauthorized access, misuse, or breaches. This commitment builds trust and fosters strong customer, employee, and stakeholder relationships.
Harnessing the Value of Data Integration
Data integration empowers organizations to gain comprehensive insights, drive innovation, and enhance operational efficiency. Organizations can uncover valuable patterns, correlations, and trends that inform decision-making by combining diverse datasets. The integration enables organizations to derive maximum value from their data assets.
Implementing Privacy-Enhancing Technologies
Privacy-enhancing technologies are crucial in preserving data privacy while enabling integration. Techniques like data anonymization, encryption, and secure data-sharing protocols protect privacy during integration processes. By anonymizing or de-identifying sensitive data, organizations can mitigate the risk of exposing personal information while still harnessing the utility of integrated datasets.
Applying Privacy-by-Design Principles
Incorporating privacy considerations from the outset through privacy-by-design principles ensures privacy protection throughout data integration practices. Organizations embed privacy safeguards into their processes by proactively addressing privacy concerns during system design and development. This approach aligns data integration with privacy regulations and industry best practices.
Enforcing Granular Access Controls
Enabling granular access controls helps strike a balance between data integration and privacy. By granting access privileges on a need-to-know basis and implementing strong authentication mechanisms, organizations limit access to sensitive information while facilitating necessary data sharing for integration purposes. Role-based access controls, data sharing agreements, and data usage policies further enhance privacy and enable data integration to coexist.
Complying with Privacy Regulations
Staying compliant with privacy regulations is vital. Organizations must understand and adhere to relevant laws such as the General Data Protection Regulation (GDPR) or the California Consumer Privacy Act (CCPA). Compliance ensures that privacy obligations are met throughout the data integration process. It builds trust, minimizes legal risks, and enhances the organization’s reputation.
The significance of Uniquely Identifying Data (UID) in data management cannot be overstated. Organizations can ensure data integrity, streamline data integration, enhance data security, and facilitate efficient data analysis and retrieval by assigning distinct identifiers to individual data elements. UID enables organizations to track and link data effectively, fostering comprehensive insights and informed decision-making.
Frequently Asked Questions (FAQs)
-
Q1: What is Uniquely Identifying Data (UID)?
A1: Uniquely Identifying Data (UID) refers to the process of assigning distinct identifiers or markers to individual data elements. These identifiers help track, link, and manage data effectively, ensuring data integrity, accuracy, and traceability.
-
Q2: Why is UID important in data management?
A2: UID is essential in data management for several reasons. It helps maintain data integrity by preventing errors and inconsistencies. UID enables efficient data integration by facilitating data matching and linking. It enhances data security by enabling granular access controls and traceability. UID also streamlines data analysis and retrieval processes, promoting operational efficiency.
-
Q3: How does UID contribute to data privacy and security?
A3: UID plays a role in data privacy and security by enabling granular access controls. Organizations can enforce access policies at the level of individual data elements, ensuring that only authorized individuals can access sensitive information. UID also facilitates traceability, making it easier to identify and mitigate potential privacy risks in case of data breaches or unauthorized access.
-
Q4: What are the challenges in balancing data privacy and integration?
A4: Balancing data privacy and integration involves finding the right equilibrium between utilizing data for insights and protecting individuals’ privacy rights. The challenges include implementing privacy-enhancing technologies, ensuring compliance with privacy regulations, designing systems with privacy-by-design principles, and striking a balance between data sharing for integration purposes and maintaining privacy safeguards.
-
Q5: How can organizations strike the right balance between data privacy and integration?
A5: Organizations can strike the right balance by implementing privacy-enhancing technologies like data anonymization and encryption, adhering to privacy-by-design principles from the outset, enforcing granular access controls, and complying with privacy regulations. Organizations can effectively integrate data while respecting privacy rights by taking a privacy-centric approach and ensuring data protection measures are in place.
-
Q6: What are the benefits of successfully managing UID in data management?
A6: Successfully managing UID in data management brings numerous benefits. It improves data quality and accuracy, enhances operational efficiency through streamlined data integration and analysis, strengthens data security and access control, and supports compliance with privacy regulations and data governance frameworks. Effective UID management enables organizations to unlock the full potential of their data assets and make informed decisions based on reliable and comprehensive insights.
-
Q7: How does UID contribute to data governance?
A7: UID contributes to data governance by enabling traceability, accountability, and auditing. Organizations can track data elements and link them to specific individuals or entities, ensuring transparency and compliance with data governance frameworks. UID facilitates effective data management practices, supports quality initiatives, and promotes responsible data usage throughout its lifecycle.